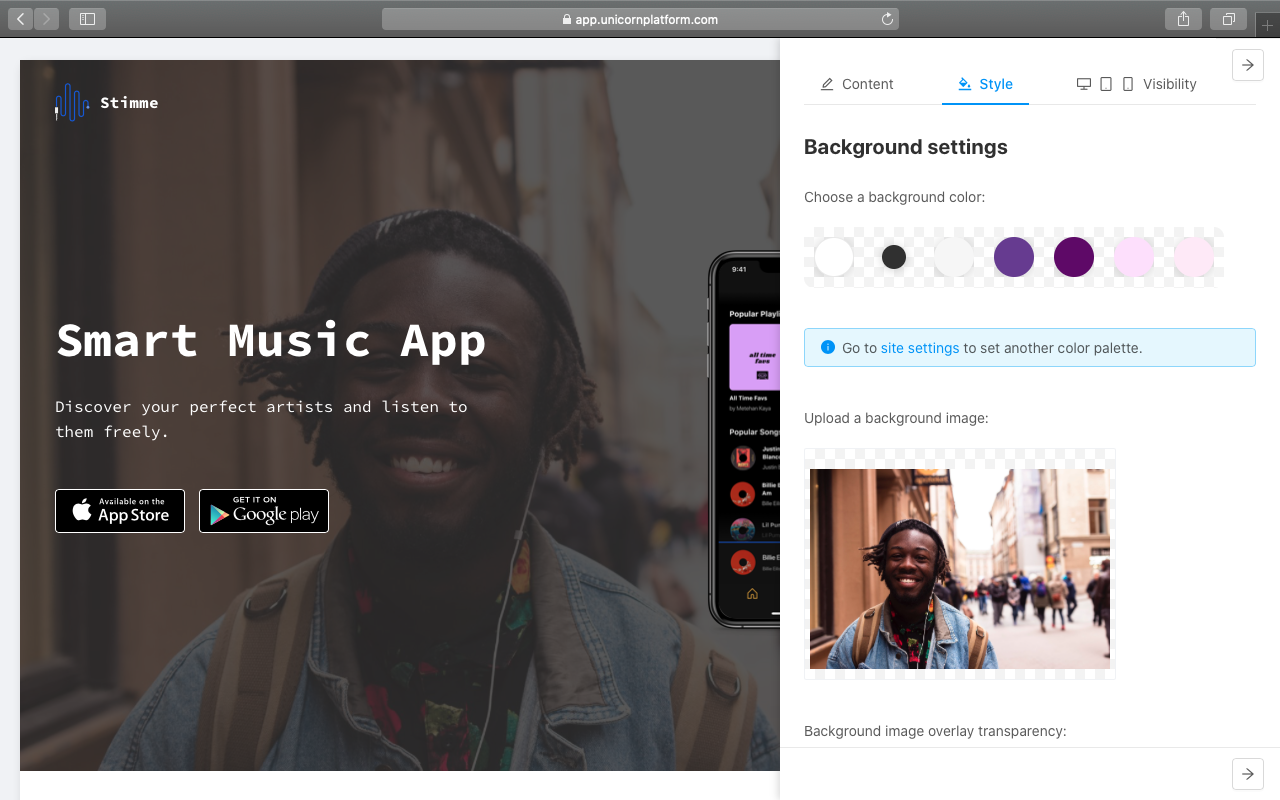
This used to be a Unicorn Platform website 🤔
This domain is connected to Unicorn Platform.
But the owner's plan does not support custom domains.
If you are the owner of this domain, kindly upgrade to a paid plan to restore the custom domain connection.